Zero-Crash Security: Protecting Legacy OT Without the Risk
Secure your older PLC assets and AI infrastructure using passive vulnerability management that identifies threats against global CVE databases without the risk of crashing sensitive hardware.
2/26/20263 min read
Secure the Core: Vulnerability Management for the OT Minefield
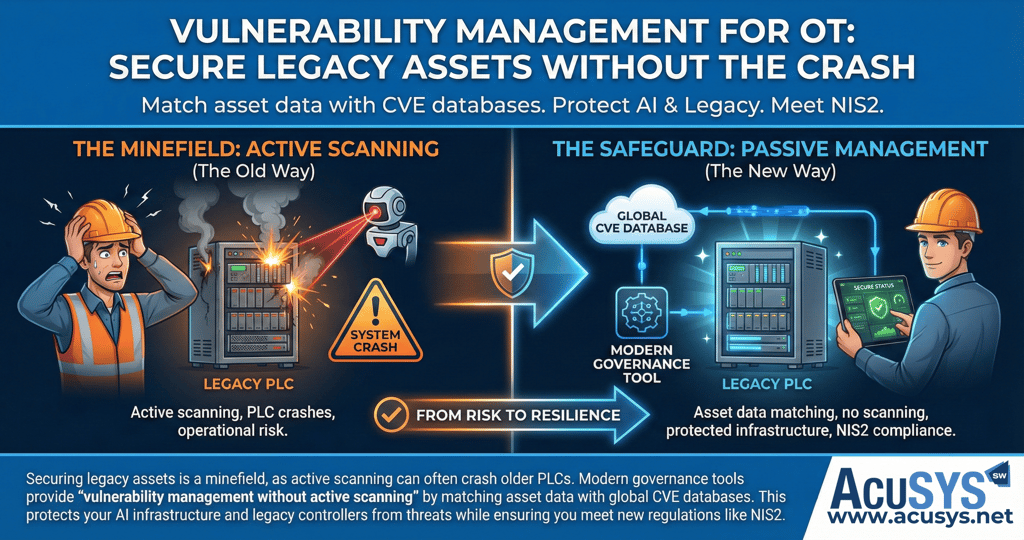
Securing a modern industrial facility is often described as navigating a minefield. On one side, you have the increasing threat of cyberattacks and the pressure of new regulations like NIS2. On the other, you have the physical reality of the shop floor: a heterogeneous landscape of legacy PLCs, sensitive sensors, and aging controllers that keep production moving.
For many IT professionals, the standard response is "active scanning"—pinging every device on the network to find weaknesses. In an OT environment, this is a dangerous gamble. Active scanning can easily overwhelm older, low-bandwidth PLCs, potentially causing a CPU crash that halts an entire production line.
To protect your AI infrastructure and legacy assets without risking your uptime, you need a strategy for vulnerability management without active scanning.
The Passive Approach: Matching, Not Probing
The most effective way to secure a "sensitive" or legacy-rich environment is through passive identification. Instead of sending intrusive packets to a device, the system uses the detailed asset inventory already captured during your automated backup process. By matching this data—firmware versions, hardware models, and serial numbers—with global CVE (Common Vulnerabilities and Exposures) databases, you can identify security gaps without ever touching the live process.
How Our Software Solutions Secure Your OT Environment
1. Vulnerability Management at the Core: octoplant
octoplant serves as the primary "governance" layer for your OT security. It embeds protection directly into the automation layer rather than just focusing on the network perimeter.
CVE Integration & Risk Scoring: octoplant provides deep visibility into missing patches and outdated firmware by automatically matching your device data with global CVE lists. It uses CVSS (Common Vulnerability Scoring System) scores to prioritize risks, letting you know which vulnerabilities are critical and which can wait for the next planned maintenance window.
Change Detection: It tracks unauthorized edits and misconfigurations to your control logic. Every change is automatically captured in backup versions, ensuring that an accidental change or a malicious "logic drift" is detected instantly.
Compliance for NIS2: octoplant supports the strict requirements of the EU’s NIS2 directive by providing structured asset visibility, transparent documentation, and a defensible audit trail of every change made to your system.
2. Building a Resilient Data Foundation: TANI & OPC Router
Security is only as good as the data feeding it. To ensure your asset inventory is accurate, you need a high-performance connectivity layer.
Secure Translation: The TANI PLC Engine acts as a secure, "multilingual translator," reading data from legacy Siemens S5 or Modbus devices and converting it into semantic-rich, encrypted OPC UA streams.
Regulated Data Flow: OPC Router uses visual workflows and the Model Context Protocol (MCP) to regulate which data is transferred to higher-level AI models or reports, ensuring that sensitive shop-floor data is only shared with authorized systems.
3. Forensic Analysis and Situational Awareness: ProcessVue
If a security incident or an unexplained trip occurs, you need to know the "why" immediately.
Sequence of Events (SOE): ProcessVue acts as a forensic analyzer, consolidating alarm and event messages from disparate systems into a unified SQL database. This allows you to perform root-cause analysis in minutes, distinguishing between a hardware failure and a potential unauthorized system access.
4. The Last Line of Defence: Rapid Recovery
True resilience is measured by how fast you recover. If a cyberattack or hardware fault occurs, downtime can cost upwards of $84,000 per hour.
Set it and Forget it Backups: octoplant keeps your operations resilient by allowing you to restore the "approved version" of a device configuration in a couple of clicks, preserving uptime and operational continuity across multiple plants.
The Bottom Line: You don't have to choose between cybersecurity and uptime. By implementing a passive, governance-based approach to vulnerability management, you can protect your legacy assets, meet regulatory mandates, and build a secure digital core for the era of Industrial AI.
Blog Summary
This post explores the "OT minefield" of securing legacy industrial assets where active scanning can cause system crashes. It explains how manufacturers can achieve vulnerability management without active scanning by using octoplant to match asset data with global CVE databases and prioritize risks with CVSS scores. By combining this with TANI for secure connectivity, OPC Router for regulated data flow, and ProcessVue for forensic analysis, organizations can meet NIS2 requirements and ensure rapid recovery from disruptions while protecting their AI-ready infrastructure.
Copyright 2026 AcuSYS Software Solutions (Pty) Ltd. All Rights Reserved.
