Engineering Freedom: The Power of Web-Native Visualization
Harness the flexibility of HTML5 and SVG to build responsive, plugin-free dashboards that provide seamless access across devices without sacrificing industrial-grade security.
2/12/20262 min read
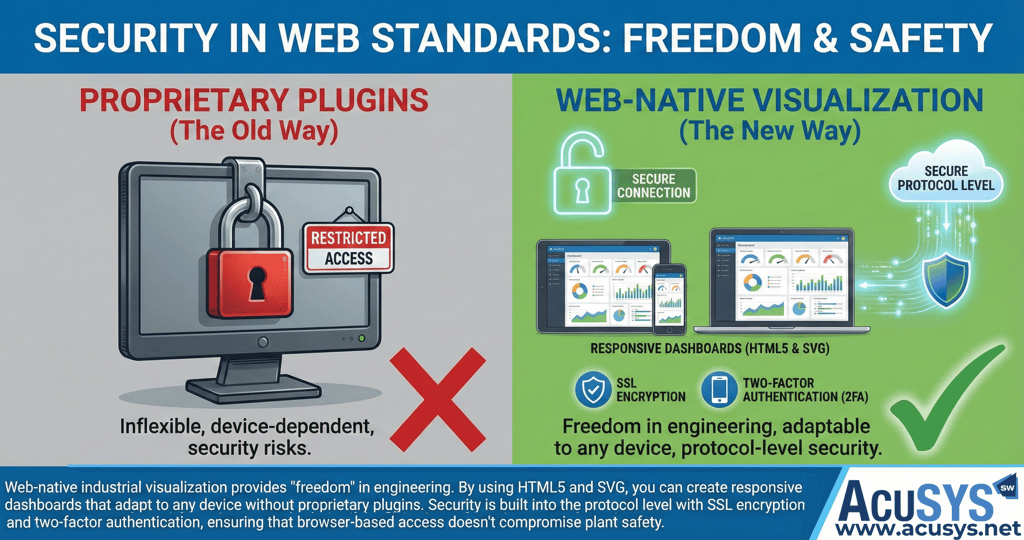
Security in Web Standards: Why Web-Native Doesn't Mean Vulnerable
In the traditional industrial landscape, "remote access" was often viewed with suspicion. For years, the only way to achieve it was through clunky, proprietary plugins—like Flash, Silverlight, or Java applets—that were difficult to maintain and frequently riddled with security vulnerabilities.
Today, the shift toward web-native industrial visualization has changed the game. By utilizing universal standards like HTML5, CSS3, and SVG, organizations gain "freedom" in engineering without sacrificing plant safety. Here is how modern web standards provide a secure foundation for the future of industrial AI and monitoring.
1. Engineering Freedom through HTML5 and SVG
The move to native web technology allows for a "Pure Web" approach where the browser on any device—smartphone, tablet, or industrial HMI—is the only client you need.
Responsive Dashboards: Using HTML5 and CSS, developers can create responsive designs that automatically adapt to any screen resolution.
Vector Precision: By using Scalable Vector Graphics (SVG), process images can be scaled infinitely without any loss of definition. This ensures that high-resolution data visualization is available on everything from low-end displays to full-blown control stations.
Community Support: Basing your operations on these standards means you benefit from a global community of developers constantly adjusting the tech to the latest state of the art.
2. Security at the Protocol Level (SSL & TLS)
A common misconception is that "browser-based" means "open to the internet." In reality, modern web-native SCADA solutions are built to be "safe as a bank."
Encrypted Communication: Data exchange is protected via SSL/TLS encryption, ensuring that information flowing between the server and the browser cannot be intercepted or tampered with.
OPC UA Integration: By implementing open industry standards like OPC UA, security is embedded directly into the protocol core. This includes built-in mechanisms for session recovery, data buffering, and secure industrial data exchange.
3. Fine-Grained Access and Two-Factor Authentication (2FA)
Security in a web-native environment is about more than just encryption; it’s about strictly controlling who can see and change specific data points.
Identity Verification: Modern systems support Two-Factor Authentication (2FA), requiring more than just a password to gain access to critical controls.
Role-Based Access Control: Using fine-grained permissions (often based on OPC UA Rights), administrators can define exactly which users or groups have the right to modify, approve, or merely view configurations. This ensures that a technician on the floor sees exactly what they need, while a director sees high-level KPIs, and unauthorized users see nothing at all.
4. Eliminating the "Plugin" Risk
One of the greatest security upgrades of web-native visualization is what it removes. By eliminating the need for third-party plugins or additional software installations, you remove a massive attack surface. There is no client-side software to patch, no outdated plugins to exploit, and no complex firewall setups required for remote workers.
The Bottom Line: Web-native visualization provides the scalability and flexibility needed for an AI-integrated facility while maintaining the highest security standards. It allows you to move away from "islands of automation" toward a unified, secure, and responsive digital core.
Blog Summary
This post explores the security and engineering benefits of web-native industrial visualization. By utilizing universal standards like HTML5 and SVG, manufacturers can create responsive, high-definition dashboards accessible on any device without proprietary plugins. It explains how security is baked into the foundation through SSL/TLS encryption, OPC UA compliant access controls, and Two-Factor Authentication (2FA), ensuring that browser-based access enhances operational flexibility without compromising plant safety.
Copyright 2026 AcuSYS Software Solutions (Pty) Ltd. All Rights Reserved.
